Cloud Busting: Cloud Forensics Workshop and Challenge (Kerry Hazelton) Friday 9a-5p
What, exactly, is “the Cloud”? Is it a network of machines connected via the Internet scattered all over the globe? Is it a data center environment located in the United States or anywhere in the world? Is it really just “someone else’s computer”? Or, is there more to it that needs to be understood by the Information Security professional, to arm him or her with enough knowledge to answer the tough question that inevitably will be asked by their employer, “Why should we take the risk to move our most sensitive data into the cloud?” To take it one step further, should in the event of a data breach that same employer should say, “We need to investigate how this happened;” what exactly will the Information Security professional need to know to successfully conduct a digital forensic investigation, especially if he or she doesn’t have direct access to the server or hardware?
The Cloud Forensics Challenge team (@Cloud4n6) is excited to come to the BSides NoVA conference for 2019 and bring our workshop with us. We have presented this training at both the 2017 BSides DC and the 2018 BSides Charm events, and seats have sold out both times. The focus of our workshop is two-fold: first, to explore key concepts of Cloud computing and understanding the procedures and processes of conducting a digital forensics investigation in the Cloud; and second, a half-day challenge to test students’ comprehension of the material and their skill sets by investigating a digital image of a Cloud-based server and searching for various “flags” to be turned in as part of a team competition. Prizes will be up for grabs and we look forward to sharing our knowledge with attendees!
What to expect: Everything including the kitchen sink. Come get a 10,000-foot view on cloud computing and how it changes the way a digital forensics investigation is conducted. Come test your skills and knowledge on log analysis, file carving, packet analysis, memory analysis, reverse engineering, steganography, cryptography, and other areas as you conduct your investigation accordingly.
What to bring: A laptop capable of running the latest version of Kali Linux. Don’t like it nor care for it? Have the following tools pre-loaded and ready to go:
- TSK/Autopsy
- Wireshark
- Volatility or other memory forensics software
- OpenStego or other steganography software
- Ida Pro (trial version is fine), Ollydbg, or other reverse engineering tool
- Decrypter or other decryption software
- Cipher tools
Trainer:

Kerry Hazelton
(Senior Cloud Security Engineer at Tenable)
Kerry Hazelton’s career between Information Technology and Security has spanned the course of over twenty years, and with it he has developed considerable experience with systems and network support, data center operations, and information security. As such, he considers himself a “cybersecurity enthusiast” due to his desire and motivation to read up on the latest trends within the industry, to learn about a new exploit or tool, or his willingness to teach and share with others his experiences over the years. He also has presented technical workshops on the tools and procedures often used in security analysis and cloud-based digital forensics at prior conferences including BSides Charm, DC, and NoVA; which helped to form the basis for the Cloud Forensics Challenge he currently runs. Additionally, he recently gave a talk at his hometown inaugural BSides Idaho Falls conference about his experiences as an instructor, and the importance of mentoring the next generation of hackers.
No Disassembly Required (Brian Satira) Friday 9a-5p
Does malware analysis seem like an arcane process involving hours of staring at assembly in OllyDbg or IDA? Is the only alternative relying on an “auto-magically” generated report from a sandbox? Many of the malware variants that today’s analyst will face during incident response, however, are not compiled binaries like Windows PE files, and do not require a knowledge of assembly to manually analyze. The goal of our training is to equip frontline defenders, regardless of job title, with skills to begin more advanced analysis of common malware variants, and help them avoid over-reliance on automated tools that may be defeated by anti-forensics.
We will present techniques for analyzing obfuscated VBA/VBS downloader scripts embedded in phishing email attachments. We will demystify malicious PowerShell being used for post-exploitation activities. We will also discuss JavaScript drive-bys and how an adversary can try to regain a foothold via a PHP tiny webshell. This training is for anyone on a blue team without a dedicated malware analyst, or anyone interested in malware analysis, but intimidated by all that hex.
Trainer:

Brian Satira is an information security researcher with ten years of experience including working for DHS and DoD as a malware analyst. Brian is an active member of I Am The Cavalry, and co-founder of Project Gunsway. Brian is also a graduate of the University of Pittsburgh and a U.S. Army veteran. Offline, Brian enjoys locksport and is both a registered locksmith in Virginia and a co-founding member of NOVA TOOOL chapter.
CTF4NOOBS (Marcelle Lee AND Tyrone E. Wilson) Saturday 8a-12p
Trainers:

Marcelle Lee is a threat researcher with WhiteOps, an adjunct professor in digital forensics and network security, and she also provides security consulting and training services through her company, Fractal Security Group, LLC. She specializes in network traffic analysis, malware analysis, phishing, and threat hunting. She is involved with many industry organizations, working groups, and boards, including the Women’s Society of Cyberjutsu, the NIST Cyber Competitions Working Group, and the Cybersecurity Association of Maryland Advisory Board. She also both builds and participates in cyber competitions, and shares her work through her Github site, https://marcellelee.github.io/.
Marcelle has earned the CISSP, CSX-P, GCFA, GCIA, GCIH, GPEN, GISF, GSEC, GCCC, C|EH, CCNA, Security+, Network+, and ACE industry certifications. She holds four degrees, including a master’s degree in cybersecurity. She has received the Chesapeake Regional Tech Council Women in Tech (WIT) Award and the Volunteer of the Year award from the Women’s Society of Cyberjutsu. Marcelle frequently presents at conferences and training events, and is an active volunteer in the cybersecurity community.
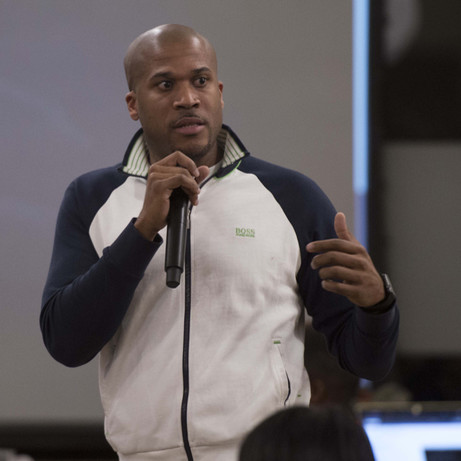
An information security professional with 20+ years of experience in information technology. Wilson also has extensive knowledge in computer network defense, vulnerability assessments, cyber threat analysis, and incident response. Currently, Wilson is the Founder and President of Cover6 Solutions, LLC; which teaches companies and professionals various aspects of information security, penetration testing, and IPv6. Additionally, Tyrone is the organizer of a 6,000+ person meetup group called The D.C. Cyber Security Professionals Founded in 2012, the D.C. Cyber Security Professionals Group’s dedication to providing networking opportunities, informative discussions and educational sessions on all things cyber, has allowed the group to grow strong while providing a real benefit to the cyber community. As an active speaker and trainer, Wilson also specializes in Intro to Cyber, Pentester Prep, and SOC Analyst Prep workshops which teaches active network defense skills while providing a path to a successful information security career.
Traffic Analysis Workshop – Beware Those Windows Infections! (Brad Duncan) Saturday 1:30p-5:30p
This workshop focuses on infection traffic for hosts running Microsoft Windows. It begins with setting up Wireshark and identifying hosts in network traffic. Participants review malware infections and learn tips to identify indicators of malicious activity. The training ends with an evaluation where participants review a pcap with malicious traffic then draft an incident report.
Trainer:

Brad Duncan specializes in traffic analysis of malware and suspicious network activity. After more than 21 years of classified intelligence work for the US Air Force, Brad transitioned to cyber security in 2010. He is currently a Threat Intelligence Analyst for Palo Alto Networks Unit 42. Brad is also a volunteer handler for the Internet Storm Center (ISC) and has posted more than 140 diaries at isc.sans.edu. He routinely blogs technical details and analysis of infection traffic at www.malware-traffic-analysis.net, where he’s provided over 1,600 malware and pcap samples to a growing community of information security professionals.

